
Blog Series
SQL 2012 AlwaysOn Failover Cluster for vCenter
vSphere 5.5 Install Pt. 1: Introduction
vSphere 5.5 Install Pt. 2: SSO 5.5 Reborn
vSphere 5.5 Install Pt. 3: vCenter Upgrade Best Practices and Tips
vSphere 5.5 Install Pt. 4: ESXi 5.5 Upgrade Best Practices and Tips
vSphere 5.5 Install Pt. 5: SSL Deep Dive
vSphere 5.5 Install Pt. 6: SSL Certificate Template
vSphere 5.5 Install Pt. 7: Install SSO
vSphere 5.5 Install Pt. 8: Online SSL Minting
vSphere 5.5 Install Pt. 9: Offline SSL Minting
vSphere 5.5 Install Pt. 10: Update SSO Certificate
vSphere 5.5 Install Pt. 11: Install Web Client
vSphere 5.5 Install Pt. 12: Configure SSO
vSphere 5.5 Install Pt. 13: Install Inventory Service
vSphere 5.5 Install Pt. 14: Create Databases
vSphere 5.5 Install Pt. 15: Install vCenter
vSphere 5.5 Install Pt. 16: vCenter SSL
vSphere 5.5 Install Pt. 17: Install VUM
vSphere 5.5 Install Pt. 18: VUM SSL
vSphere 5.5 Install Pt. 19: ESXi SSL Certificate
Permalink to this series: vexpert.me/Derek55
Permalink to the Toolkit script: vexpert.me/toolkit55
At this point I’ll assume you’ve been following this series and ran my Toolkit script to create all of your certificates.
VUM SSL Configuration
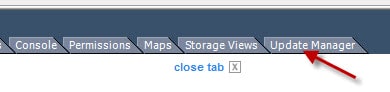
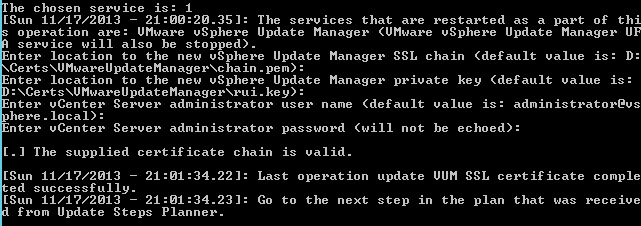
1. Run the VMware Certificate automation tool script and from the main menu select option 8. On the VUM menu select option 1.
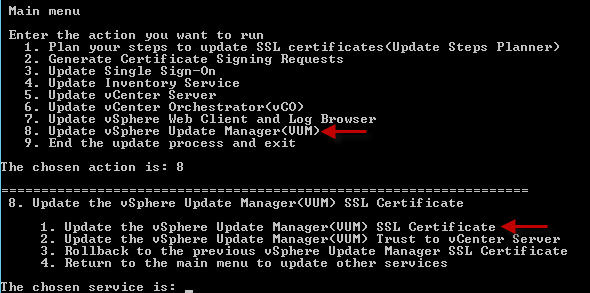
2. After selecting option 1 from the VUM menu you will be prompted for a series of responses. The chain.pem and rui.key paths should already be set, via my Toolkit script (Option 4). Enter the Administrator password you used during the SSO installation, many installments ago. Sit back and wait a couple of minutes, and you should see a successful message.
VUM Configuration
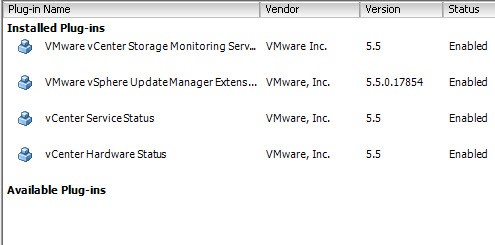
1. Launch the VMware vSphere Windows client and connect to your vCenter server. If you haven’t already installed the VUM plug-in, go to the Plug-ins menu and you should see a plug-in under “Available Plug-ins”. Click Download and Install. Run the installer using all default values. You can see below that I’ve already installed the extension.
2. After the Assuming the install goes well close the vSphere client. Reconnect to vCenter using the Windows vSphere Client. You should NOT get a SSL warning for vCenter or VUM. If you do get a SSL warning, something went wrong, or you also installed another service like Auto Deploy or a third-party plug-in that is untrusted.
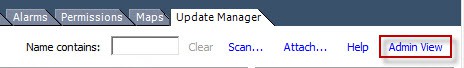
 3. Depending on your server hardware vendor, you may want to add the HP depot URL to VUM so know when they release updated software. Unfortunately at this time I’m not aware of a Cisco VIB depot. Open the Admin View of VUM.
3. Depending on your server hardware vendor, you may want to add the HP depot URL to VUM so know when they release updated software. Unfortunately at this time I’m not aware of a Cisco VIB depot. Open the Admin View of VUM.
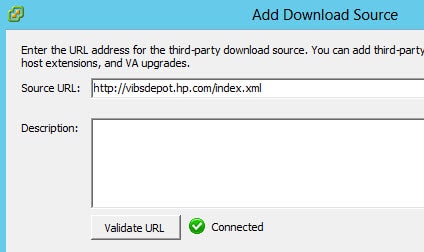
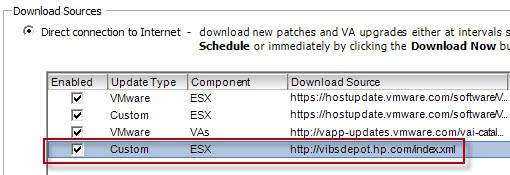
4. Once the VUM Admin page opens click on the Configuration tab. Select Download Settings. Click Add a Download Source and use the following URLs:
HP: http://vibsdepot.hp.com/index.xml
Dell: http://vmwaredepot.dell.com/index.xml
After you add the URL(s) it will appear the list. Click on the Download Now button. Monitor the Recent Tasks pane and wait for the download to complete.
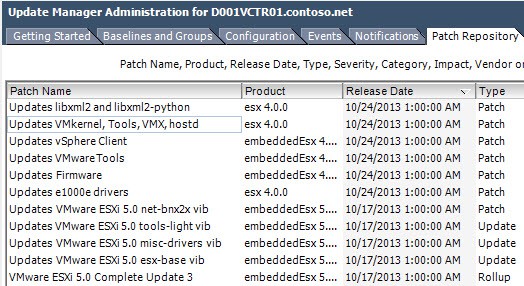
5. After a bit of time your patch repository will be fully populated.
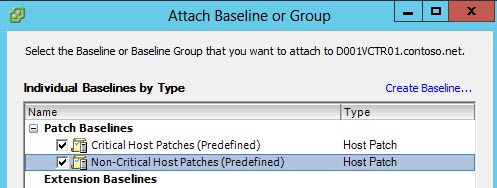
6. Next up I would suggest attaching VUM baselines to both your hosts and VMs. In the Hosts and Cluster view go to the VUM tab then attach a baseline. I’d recommend you check the two boxes shown below.
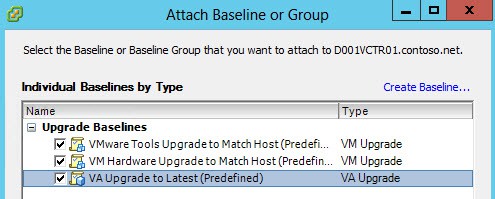
6. Switch to the VM and Templates view and attach the three provided baselines.
7. You can now perform VUM scans and check your compliance status.
VUM hasn’t undergone any visible changes in vSphere 5.5. So if you are accustomed to using VUM in previous releases, then you won’t have anything new to learn. You could also schedule weekly compliance scans and have reports emailed to you. One could also create custom baselines that are static, so that when new patches are downloaded you aren’t instantly out of compliance. VMware has stated VUM is dying, so I suspect in the 6.0 timeframe we will see an entirely new way to handle patches.
Next up in Part 19, learn how to update your ESXi host certificate.





Great series. it helps me a lot to upgrade our vsphere to 5.5. Thanks
I replaced all the certificates as described and everything is issued by my CA. When going to update manager, I receive no warning.
When I attempt to upload a new host ESXi image in VUM, I'm presented with a stock VMware SSL certificate. I can't figure out what certificate is being presented. Just issued by VMware.
E = [email protected]
CN = VMware
OU = 'VMware Inc.'
O = 'VMware Inc.'
L = CA
S = CA
C = US
All services are running with custom certs as far as I can tell.
yes, that is a known issue. From all appearances that is a built-in cert that users cannot change.
I didn't know about the HP VIB download source. Thanks for including that!