
If you recall the vCenter 5.1 installation order, you will realize they’ve now moved up the web client install. This was done consciously so you could troubleshoot/configure the SSO service prior to vCenter being installed. Great idea VMware!
Blog Series
SQL 2012 AlwaysOn Failover Cluster for vCenter
vSphere 5.5 Install Pt. 1: Introduction
vSphere 5.5 Install Pt. 2: SSO 5.5 Reborn
vSphere 5.5 Install Pt. 3: vCenter Upgrade Best Practices and Tips
vSphere 5.5 Install Pt. 4: ESXi 5.5 Upgrade Best Practices and Tips
vSphere 5.5 Install Pt. 5: SSL Deep Dive
vSphere 5.5 Install Pt. 6: SSL Certificate Template
vSphere 5.5 Install Pt. 7: Install SSO
vSphere 5.5 Install Pt. 8: Online SSL Minting
vSphere 5.5 Install Pt. 9: Offline SSL Minting
vSphere 5.5 Install Pt. 10: Update SSO Certificate
vSphere 5.5 Install Pt. 11: Install Web Client
vSphere 5.5 Install Pt. 12: Configure SSO
vSphere 5.5 Install Pt. 13: Install Inventory Service
vSphere 5.5 Install Pt. 14: Create Databases
vSphere 5.5 Install Pt. 15: Install vCenter
vSphere 5.5 Install Pt. 16: vCenter SSL
vSphere 5.5 Install Pt. 17: Install VUM
vSphere 5.5 Install Pt. 18: VUM SSL
vSphere 5.5 Install Pt. 19: ESXi SSL Certificate
Permalink to this series: vexpert.me/Derek55
Permalink to the Toolkit script: vexpert.me/toolkit55
Configure SSO STS Chain
For some reason the VMware certificate tool does not automatically import the trusted CA chain into the SSO STS store. So we need to manually do that. My Toolkit script creates the complex Java keystore file, which is quite tedious. See Part 8 for the low down on my vCenter 5.5 Toolkit script. So all we need to do here is import the Java keystore file. I’m opting to leave the default self-signed chain in place, just in case there is a dependency.
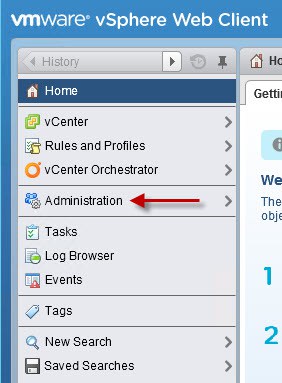
1. Login to the vSphere web client with the [email protected] account. In the left pane click Administration.
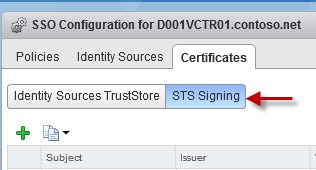
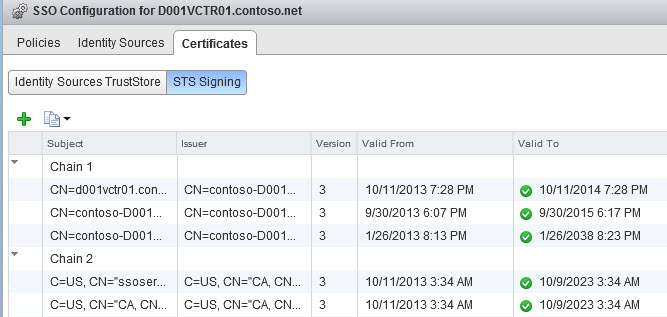
2. Under Single Sign-On click Configuration. Then click on the Certificates tab and then STS Signing.
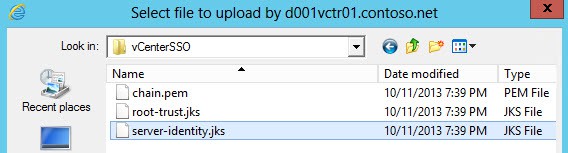
3. Click on the green Plus sign and navigate to the vCenterSSO certificate directory the Toolkit script created. Select the server-identity.jks file. When prompted for a password enter testpassword.
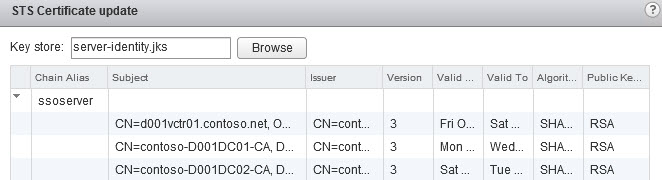
4. Depending on your CA configuration you should see two or three certificates listed. In my case I have three, since I have a root and intermediate CA. Click on the ssoserver line and then click OK. Enter testpassword again.
If the import is successful you should see two certificate chains.
5. Reboot your vCenter server so that all the services are refreshed and pickup the new certificate chain.
Add Identity Source
In vSphere 5.5 your Active Directory identity source is not automatically added. So we will need to add AD as a source so you can authenticate with domain-based accounts.
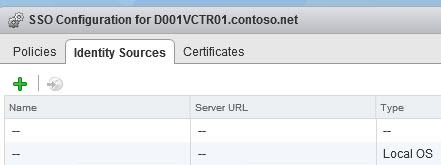
1. Login to the vSphere web client, in the left pane click on Administration. Under Single Sign-On click Configuration. Click on Identity Sources in the middle pane.
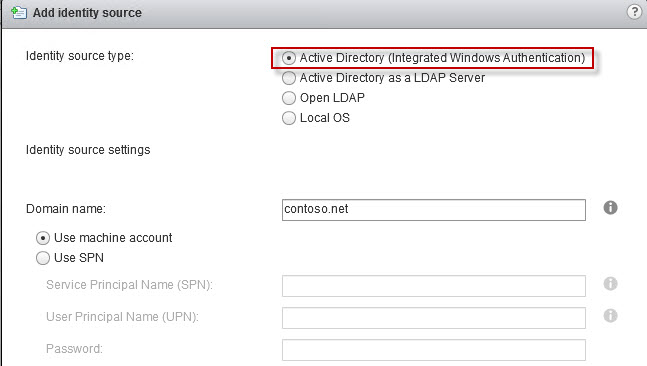
2. Click on the green plus sign. If you want rich Active Directory support then choose Active Directory (integrated Windows Authentication). Chosing Active Directory as LDAP Server is for 5.1 backwards compatibility and should NOT be used. You will have issues with domain trusts, etc. Should be avoided!
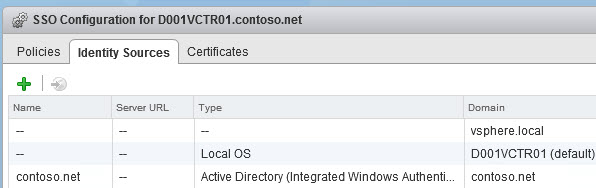
3. After the source is added you should see three Identity Sources.
Delegate SSO Admin Rights
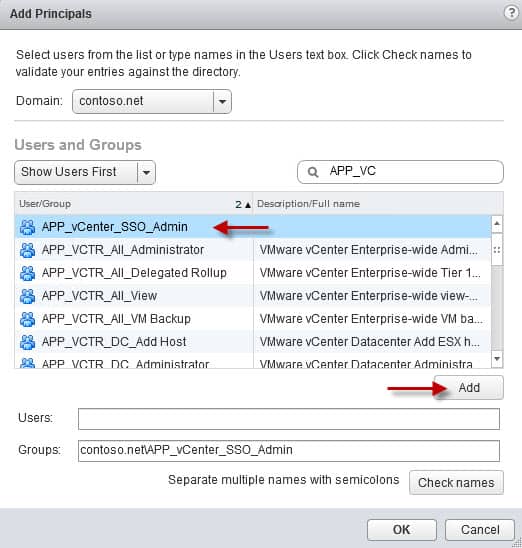
1. Create a group in Active Directory that you want to delegate SSO administrator rights too. In my case the group is called APP_VCTR_SSO_Admin. You can use whatever name you wish. Put your account into that group.
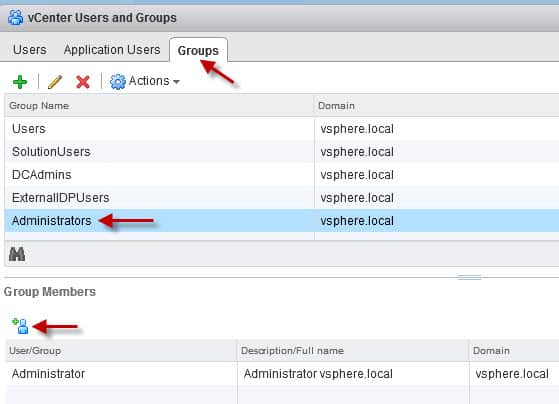
1. On the Groups tab click on Administrators, then in the lower Group Members pane click on the Blue Man Group person.
2. Change the domain to your AD domain, then find your group. Highlight the group then click on Add. Then you can click on OK to add the group.
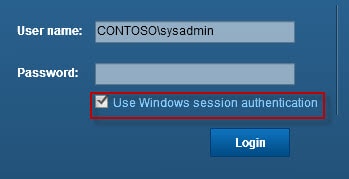
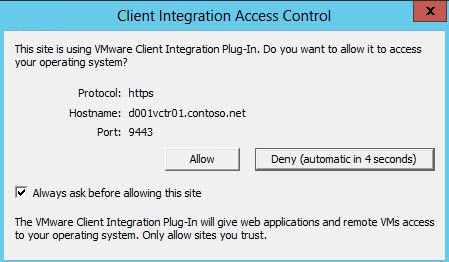
3. If you log out of Windows then log back in (to refresh your group membership), you should now be able to use the Windows credential option to access the vSphere web client. The first time you try it a warning message will likely appear. I would uncheck the Always Ask box unless you like exercising your fingers.
Summary
Configuring some basic SSO settings is not rocket science, but common to many environments. At a minimum you need to import the SSO STS certificate chain. Nearly everyone has AD, so adding the more intelligent SSO 5.5 AD identity source will be on everyone’s agenda. Shared accounts are never a good idea, so setting up a group for SSO admin delegation is a great idea.
Next up in lucky Part 13 we install the Inventory Service and secure it with trusted SSL certificates.





Fantastic series yet again Derek 🙂
It would be great if there was a GUI utility to take out all the hard work in creating certificates for both Microsoft CA and Public Authoritative ones like Verisign, Entrust, RSA.
Any guru VMware developers out there willing to take this on?
Kind Regards
VMCreator
I recently found this series of articles and wanted to thank you for making the SSL process so much easier. Amazed that VMware doesn't treat this with more seriousness and guidance.
I would like to ask if you've given any consideration to adding certificate generation for SRM. It would seem like an easy item to add.
Thank you
Before you can log in with your domain account or group don't you need to go to vCenter -> Hosts and Clusters -> Click on your vCenter Server -> Click on Manage tab on right -> Click on sub tab Permissions -> and add your group or user there as well?
Thank you for all that you do.