
Blog Series
SQL 2012 AlwaysOn Failover Cluster for vCenter
vSphere 5.5 Install Pt. 1: Introduction
vSphere 5.5 Install Pt. 2: SSO 5.5 Reborn
vSphere 5.5 Install Pt. 3: vCenter Upgrade Best Practices and Tips
vSphere 5.5 Install Pt. 4: ESXi 5.5 Upgrade Best Practices and Tips
vSphere 5.5 Install Pt. 5: SSL Deep Dive
vSphere 5.5 Install Pt. 6: SSL Certificate Template
vSphere 5.5 Install Pt. 7: Install SSO
vSphere 5.5 Install Pt. 8: Online SSL Minting
vSphere 5.5 Install Pt. 9: Offline SSL Minting
vSphere 5.5 Install Pt. 10: Update SSO Certificate
vSphere 5.5 Install Pt. 11: Install Web Client
vSphere 5.5 Install Pt. 12: Configure SSO
vSphere 5.5 Install Pt. 13: Install Inventory Service
vSphere 5.5 Install Pt. 14: Create Databases
vSphere 5.5 Install Pt. 15: Install vCenter
vSphere 5.5 Install Pt. 16: vCenter SSL
vSphere 5.5 Install Pt. 17: Install VUM
vSphere 5.5 Install Pt. 18: VUM SSL
vSphere 5.5 Install Pt. 19: ESXi SSL Certificate
Permalink to this series: vexpert.me/Derek55
Permalink to the Toolkit script: vexpert.me/toolkit55
Automated vCenter SSL
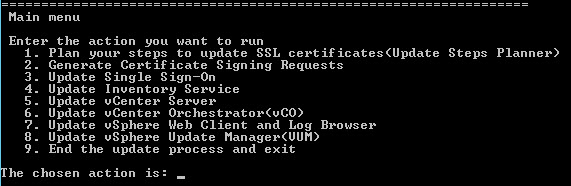
1. From an elevated command prompt run the VMware certificate automation tool. Select Option 5.
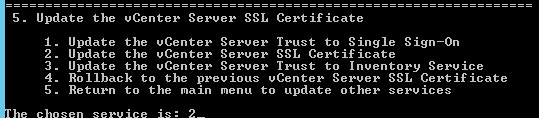
2. On the vCenter menu select Option 2.
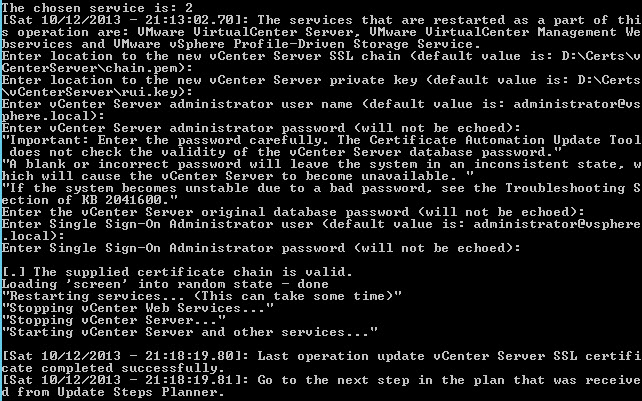
3. Answer all of the questions according to your environment. The certificate paths should already be configured if you used my Toolkit script. The vCenter server database password is the password to your vCenter service account. Make sure you enter it correctly or you may be left with a smoking vCenter hole.
Automated vCenter Orchestrator SSL
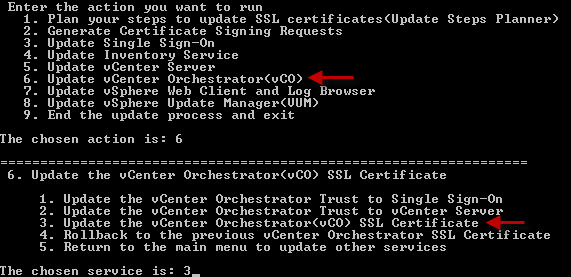
1. From the main menu select Option 6, then select option 3.
Health Check
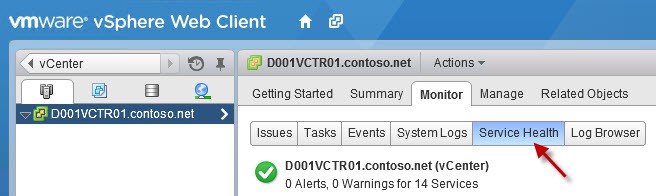
1. Login to the vSphere Web client with the [email protected] account. In the left pane click on the vCenter object. Click on Hosts and Clusters, then on the Monitor tab click Service Health.
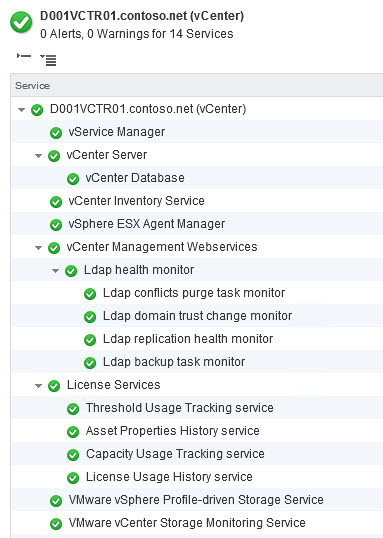
If everything went well, all services should be green. If you service list is empty, then wait a minute or two, then click on the refresh Circle/Arrow in the upper right corner. If some services are in an unhealthy state, then reboot your vCenter server. Wait 10 minutes after the reboot, then check back on this page. Profile Driven Storage was a little stubborn for me, but a reboot and patience worked.
Summary
Yes, we are finally here! You have a fully working vCenter Server on Windows Server 2012, plus all trusted SSL certificates. If all of your services came up healthy, then you should be good to go. But wait..we still have VUM to install, configure, and secure. Plus those pesky ESXi hosts all need SSL certificates too. Check out the VUM install in Part 17.





I will use that then, the script doesn't seem to work so I will wait for your blog post.
In anticipation of parts 17 and 18 of the series, here's my initial experience with installing VUM 5.5.
In the installer, on the vCenter Server Information screen, I changed the IP Address / Name field to the FQDN of the server. It was prepopulated with the server's IPv6 address. I used my vCenter service account credentials (domainuser) under Username and Password. I did not test with the [email protected] credentials. Otherwise I completed the VUM installation with the default settings.
I ran the ssl-updater.bat tool and updated the certificate and private key in the usual manner (options 8 and then 1) and rebooted the vCenter server.
I attempted to install and enable the VUM plugin in the vSphere client, but enabling the plugin failed. This issue is addressed in the KB article "Enabling Update Manager fails with the error: database unavailable or has network problems (1015223)" (http://kb.vmware.com/kb/1015223). Based on that, I reconfigured the VUM service to run under my vCenter service account, which is the dbo for its database, and restarted the service. The service runs under the local system account by default. That fixed the problem.
I'm going to move forward with configuring VUM using the guidelines in the 5.1 series at https://www.derekseaman.com/2012/09/vmware-vcenter….
FYI, successful with VUM configuration using the 5.1 series guidelines. Jeff.
Thank Derek for a great blog and thanks Jeffry, I also followed the KB and was successful with my VUM configuration with 5.5 with a separate 2012 SQL server.
Got problems with Updateing my vCenter SSL Certificate:
[10.12.2013 – 15:26:36,33]: Attempting rollback…
Could not reload vCenter SSL Certificates
[10.12.2013 – 15:26:37,77]: ""Cannot reload the vCenter Server SSL certificates. The certificate might not be unique.""
[10.12.2013 – 15:26:37,79]: Deleting the new certificates and keys…
[10.12.2013 – 15:26:37,81]: Restoring the original certificates and keys…
1 Datei(en) kopiert.
1 Datei(en) kopiert.
1 Datei(en) kopiert.
[10.12.2013 – 15:26:37,85]: The vCenter certificate update failed.
My environment:
Windows 2012 Server Fully Patched
Clean Windows Installation
Everything works fine, but on the last step im unable to Update the certification vor de vcenter server
Sounds like a possible problem with the OU value in the certificate. Did you use my Toolkit script to create all of your certificates, or did you try and re-use them?
Hi!
I did not get the script to work properly when generating certificates for the linux appliance (vCSA). To get it o work, I had to change both #$WServices to the same as #$LServices, if not the script would fail because it was lookun in the wrong folders (example: C:CertsVMware vCenter Service CertificateVMware vCenter Service Certificate.csr). As I am no guru on PowerShell, I was not able to figure out where to make the changes som that the $Service variable was correctly set (or maybe some other variable has to be changed). I will investigate further, maybe I'll figure it out and publish an update.
I'll check out the Linux section this weekend. I haven't tested that for a while, so bugs may have cropped in.
Thank you for the very thorough blog and installation instructions. I came across something strange and was wondering if yourself of the community could help. The scenario I am seeing is that when I log into the vSphere Web client as @vsphere.local I am able to see the vCenter Server, but when I log in under the Domain vCenter Service account which I have added as as the local admin, "act as part of the OS", and added to an AD Group which has been added to the Administrator's group within the vCenter Users and Groups section.