I just migrated my home firewall to a Firewalla Gold Plus (4x 2.5GbE ports) and configured it to use NextDNS. For quite some time I’ve been running NextDNS with my old OPNsense firewall. NextDNS is a cloud based DNS service that is very security and privacy oriented. It lets you configure various block lists and other security options to make web surfing safer and faster. Think of it as Pihole in the cloud, if you know what Pihole is. Tip: For the best NextDNS experience on Firewalla use this integration on Github.
After some thorough testing of Firewalla + NextDNS I found that Firewalla appeared to still be logging outbound ‘flows’ (as they call it) to the NextDNS blocked sites. I was quite puzzled as to what was going on. But before I tell you the solution, let’s look at the problem I was seeing.
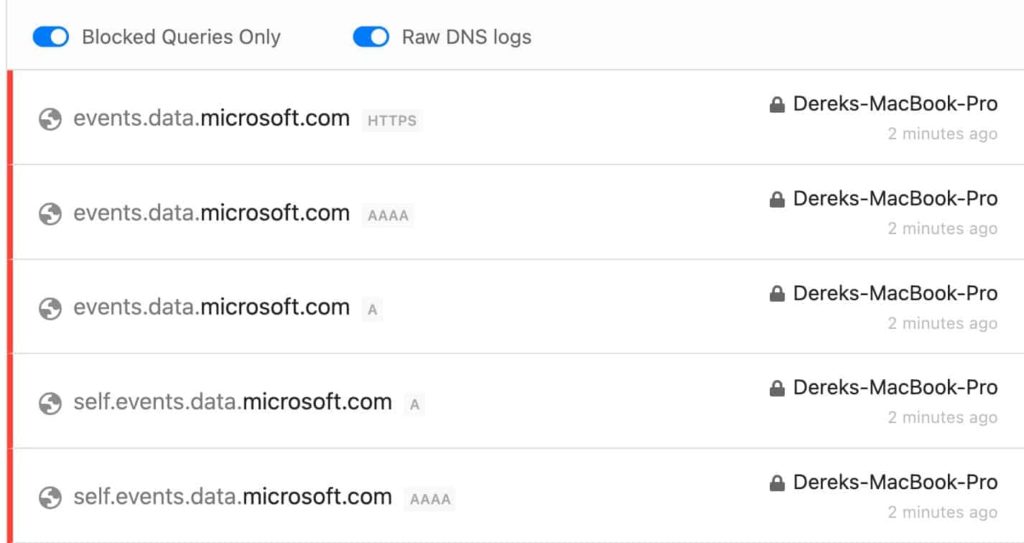
As you can see in the first graphic below, NextDNS shows that self.events.data.microsoft.com DNS query was blocked (Red bar on the left, last two DNS queries). So that should mean that Firewalla should not log any outgoing traffic to that site from my MacBook.
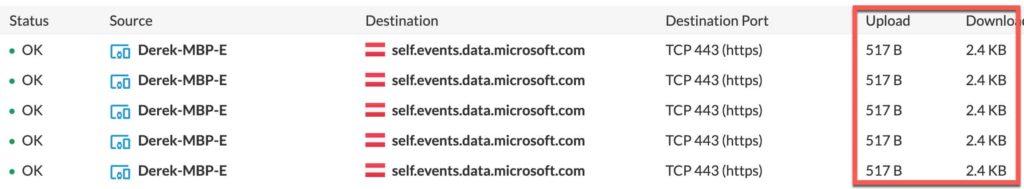
However, as you can see below, my MacBook was logged as sending and receiving data which I found very puzzling.
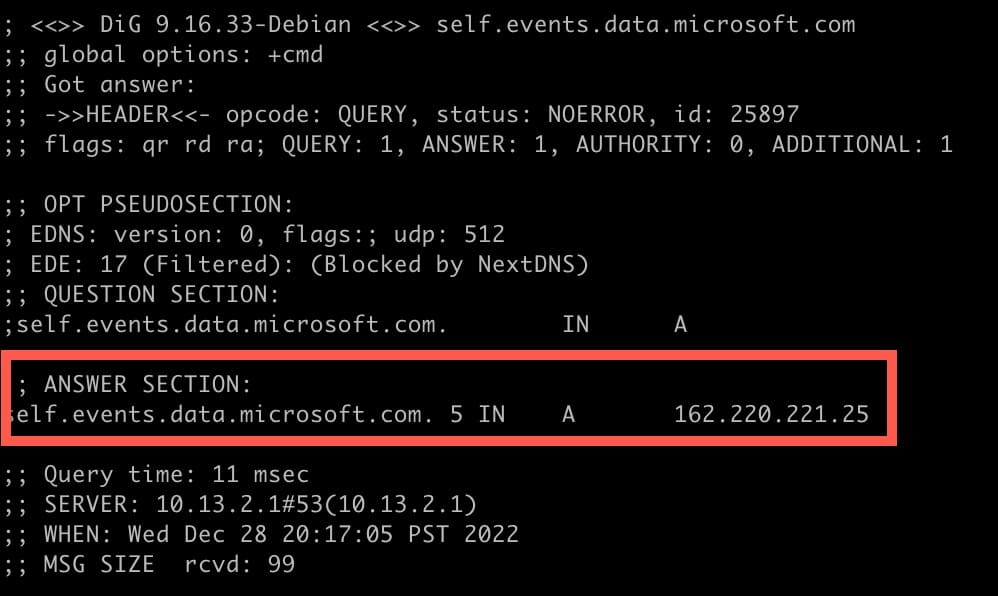
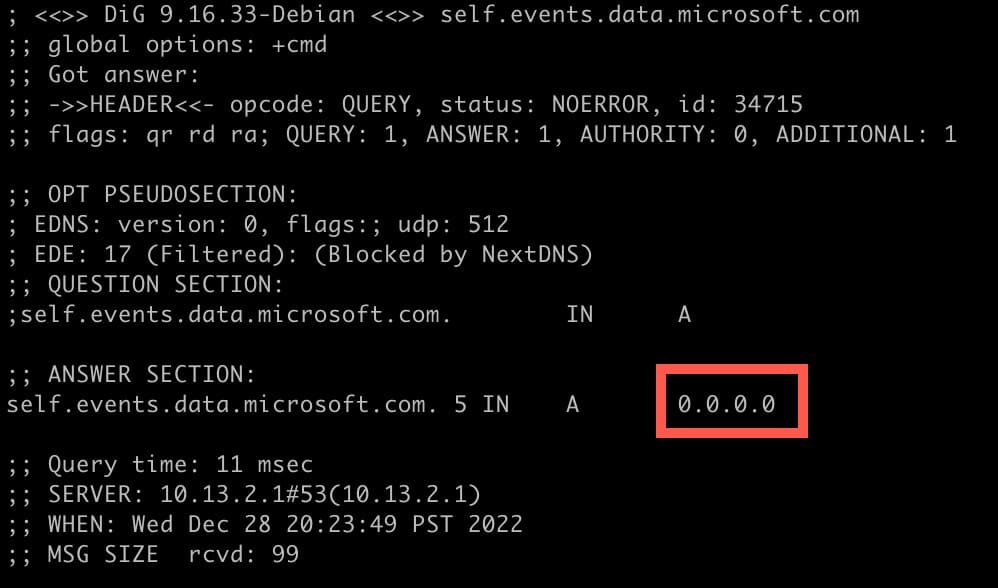
I then did a ‘dig’ on the Microsoft domain, and I was expecting NextDNS to return 0.0.0.0 as they should for a blocked domain. However, that’s not what I got back.
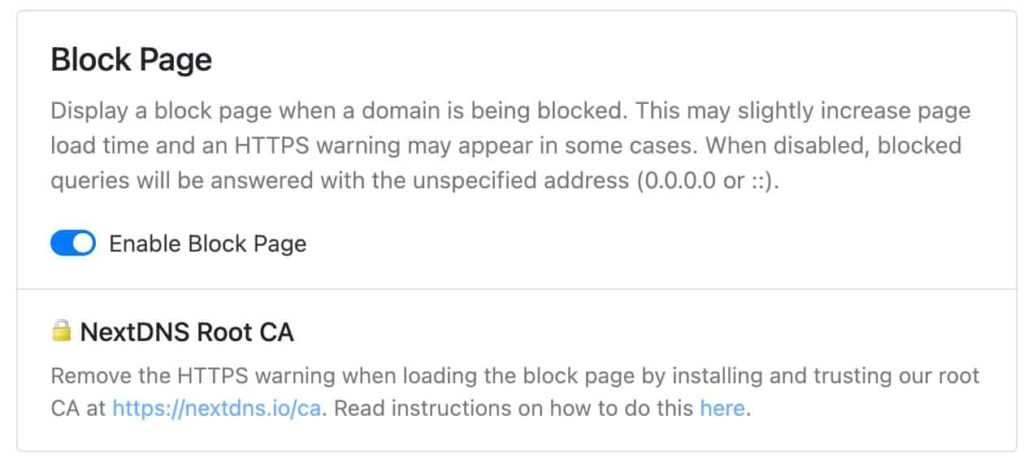
I did some research into that IP and other IPs that Dig returned for other blocked domains, and was able to deduct that those IPs belonged to NextDNS and were for their optional “blue” block notification page. This blue block page is shown in your browser when you go to a blocked site. Ah ha! So I went into NextDNS and disabled the blue blocking page.
With the blocking page disabled, I then flushed my DNS cache and re-ran the Dig, hoping to see 0.0.0.0 returned. And yes, I now got 0.0.0.0 back.
Next I went back into Firewalla Flows and looked for any entries for that Microsoft self domain. None were to be found. I then flipped back to NextDNS logs to verify blocks were happening after I disabled the block page, and there were a plethora of blocks. This validated that Firewalla did not log any Flows to blocked NextDNS domains because the host doing the lookup (my MacBook) returned 0.0.0.0 to the application so the application didn’t try to send any outbound data. My Firewalla logs are now cleaner and don’t show “odd” activity to blocked domains.
Summary
If you use NextDNS and have enabled their custom block page, then Firewalla will log all blocked domains as a successful “OK” traffic Flow. This is misleading, as no traffic was actually sent to the offending IP address of the blocked domain. Disabling the NextDNS block page then prevented the application/operating system from even attempting an outbound connection, so Firewalla saw no traffic to log.