Along with a few updates to my 2023 dream home office setup (see post here), I also felt it was the time to do a whole house network upgrade. This post covers my network “refresh” that is built to support multi-gig, 10Gbps, PoE and enterprise WiFi. Nothing was broken with my old network, but it was put together over several years and wasn’t built to support anything higher than 1Gbps networking. 2023 is the year of my network upgrade!
Existing Network Gear
Let’s set a baseline of what my old network looked like, so we can better compare it to the upgraded gear. My ISP provides symmetrical 1Gbps service. Wired speedtests top out at 940/940. For WiFi, I had three Amazon Eero 6 Pro access points. For a consumer based WiF network, Eero is fine. Not amazing, not terrible. Good for your non-techie consumers, but bad for power users.
Eero issues that bugged me:
- Little to no performance or utilization metrics
- Forces one SSID for both 2.4GHz and 5GHz networks
- Decent performance, but not amazing
- Firmware updates are forced on you at random times
- Owned by Amazon so big privacy concerns
- No advanced security or VLAN support
My next WiFi system needed to address these concerns. Now for my firewall, I was using OPNsense (open source) on a Protecli multi-NIC appliance. This solution felt more like a science project than a robust firewall solution. Yes, it is highly configurable with a zillion knobs to tweak and plugins. However, it really lacked usability and trying to do simple things required googling and a lot of trial and error. To get any type of metrics you had to bolt on a paid solution like Zenarmor. And even then alerting on suspicious traffic or new devices was non existent.
My new firewall solution needed:
- Greatly increased usability
- Commercial solution with regular user-oriented feature updates
- Wireguard VPN client and server
- 2.5Gbps WAN support
- Robust alerting for possible security issues or unusual traffic patterns
Beyond the firewall, I also wanted to upgrade my core ethernet switch and satellite switches to support multi-gig, 10Gbps, and PoE for my new WiFi access points. My existing switches were just basic managed 1Gbps switches. If cost was no object, then of course I’d go for all 10G switches everywhere. But with the number of ports I need, combined with PoE, those switches are still wildly expensive. So most ports on my refresh are 2.5G with select devices getting 10G ports.
Core 10G PoE Network Switch
For a replacement of my managed 1G “core” switch, I wanted a few features:
- 16 or more 2.5Gbps ports
- 2 or more 10Gbps copper ports
- PoE+ (802.3at) 30W (or higher)
- VLANs
- Quiet fans
- Full layer 2 management
After a lot of research, I settled on the QNAP QSW-M2116P-2T2S. Yes, QNAP, the NAS company. I didn’t know they offered switches, but they do. I looked at a lot of brands, and nothing came close to my requirements in a similar price bracket.
It features 16 Multi-gig PoE+ ports, 2 10G ports with PoE++, and 2 10G SFP ports for 20 total ports. It’s a managed switch and has a decent UI. The web UI is a bit limited (but there’s a full CLI) and one feature I miss is labeling ports and VLANs. But that doesn’t affect performance and is only cosmetic. Although QNAP isn’t the first company that comes to mind for network switches, this model hit the spot for me.
Satellite Switches
I have three “satellite” ethernet switches in my house. None of these are particularly exciting. For my home office I wanted a 10G unmanaged switch. This would enable full 2.5Gbps to my both of my MacBook Pro laptops. In the office I upgraded to the TRENDnet TEG-S750. It has 5 ports of 10Gbps, which can run at multi-gig and 1Gbps speeds as well. This is uplinked to my QNAP switch at 5Gbps. I didn’t want to push 10Gbps through my CAT5 in-wall cabling, and I don’t need more than 5Gbps anyway. This switch is mounted under my desk with a custom Protocase bracket.
I have a smart house with a number of hubs (Hubitat C8, HomeBridge, Home Assistant, Hue, Flic, etc). These hubs are co-located, so I wanted an IoT switch. For this switch I used a NETGEAR 10-Port Gigabit/10G Ethernet switch (GS110EMX). This has a 8x 1Gbps ports and two 10Gbps ports. One 10G port is uplinked to my QNAP switch.
In my home theater room I have a number of ethernet connected devices (TV, receiver, AppleTV, nVidia Shield, etc.). I also though I probably would put a WiFi AP in this room, so I also wanted a 2.5Gbps PoE switch. I chose the Netgear MS108EUP. I didn’t end up putting a WAP in this room, but it’s here for future use. It’s a managed switch, supports VLANs, trunking, variety of PoE+ and PoE++ settings, and a visually pleasing web interface. It’s passively cooled, so it’s dead silent.
Network Cables
Even though 2.5Gbps should run over CAT 5E, it can be “iffy” over longer runs. Although I’m not replacing any in-wall cables (which are CAT 5E), I did go ahead and upgrade all non-in-wall cables to CAT 6A. For all of these cables I used the Monoprice Slimrun cables. These are very slim, high quality, and come in a variety of colors and lengths. Super happy with these cables…highly recommended.
WiFi Upgrade
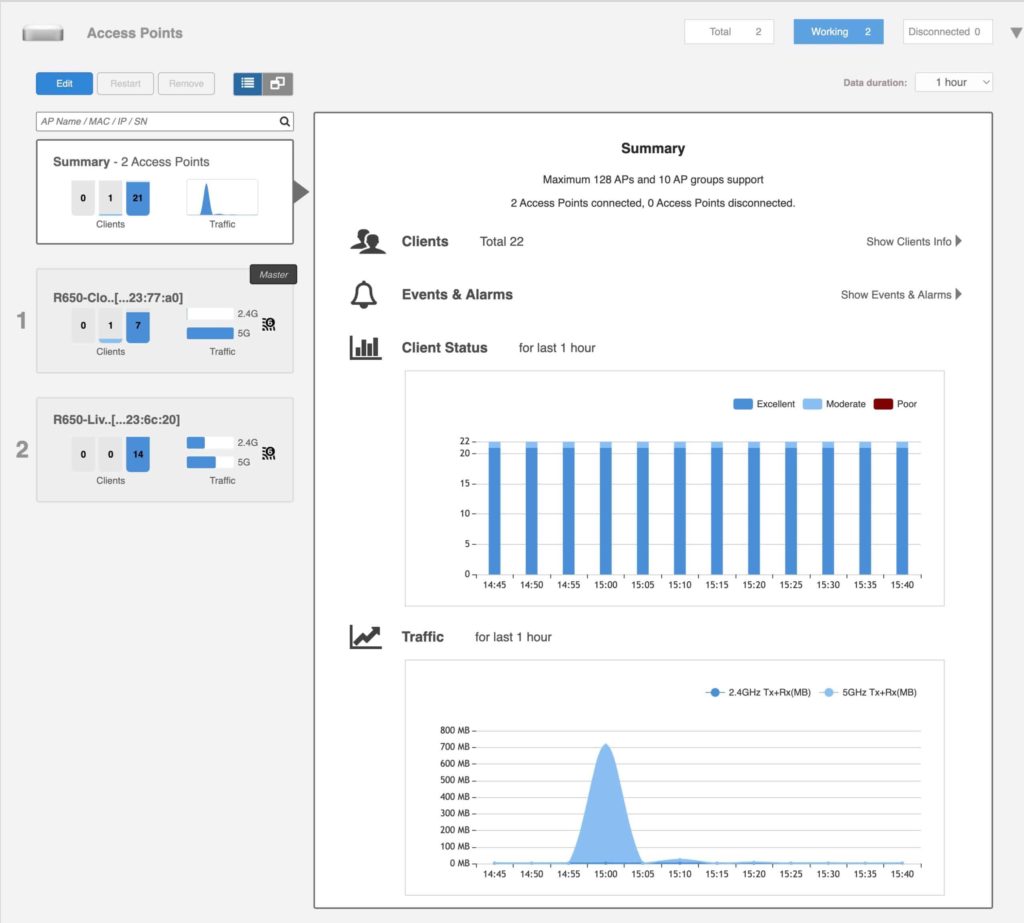
After a lot of research, mostly on Reddit, I settled on two Ruckus R650 APs. These are WiFi 6 (not 6E) APs. Now a lot of you probably haven’t heard of Ruckus, I know I hadn’t until I was doing my research. Ruckus solutions are generally aimed at businesses, large venues, hotels, etc. However, their APs can work well in residential settings using their “Unleashed” controller firmware.
Ruckus Unleashed is a firmware controller package that is free, no subscription costs, and has a great local web interface to control your WiFi network. Many, but not all, of their APs can be flashed with Unleashed. What makes Ruckus special is their patented adaptive antenna system called BeamFlex. According to a number of networking professionals, Ruckus is the best WiFi in the business. You can check out a YouTube video about their BeamFlex system here.
Why the Ruckus R650 vs. other models? Well, not all models of Ruckus APs are best suited for a low density residential environment. If you look at the R650, R750 and R850 datasheets and compare the antenna gain (max), TX power targets (per chain) and the receive sensitivity you can see that the R850’s antenna gain is the worst (2dBi vs 3dBi), the receive sensitivity is the worst, and the 5GHz transmit power per chain is worse than the R750. The 2.4 GHz transmit power per chain is also worse than the R650. The R650, with 4×4:4 5GHz, and its very long reach 2×2:2 2.4 GHz antennas, are a killer combination of speed and range for a residential setting. The “higher end” APs are best suited for high density commercial environments with hundreds or thousands of WiFi clients.
The Ruckus R550 would probably been sufficient and more economical, but isn’t as performant as the R650. I don’t plan on upgrading WiFi again for a few years (not until WiFi 7 is widely deployed), so wanted to future proof a bit. Why two APs and not just one? Well my house is about 2000 SqFt, three levels, and a stucco exterior. Due to the floor plan and other interference issues, one AP would just not cut it for good 2.4 GHz and 5 GHz coverage in all areas.
The net result of the upgrade is that my WiFi in nearly all locations is 25% to 200% faster at 5 GHz than Eero. And in some tests even pushed almost 300% faster. Not bad for both being WiFi 6, and with two Ruckus APs vs. 3 Eero 6 Pros. I might be able to do even better with more optimized AP placement, but I’m happy with my current placement.
Ruckus Unleashed is enterprise oriented and it has a lot of configuration knobs and features. The best guide for Ruckus Unleashed is by Blackwire. I followed their entire guide to the “T” with the following exceptions:
- Enabled 802.11r FT roaming
- Enabled 802.11k Neighbor-list Reporting
- Enabled Band balancing
- Configured for “Optimize for Performance”
- Set roam factor to 3 (CLI) (802.11v)
802.11r, 802.11k and 802.11v are all recommended by Apple for the best AP roaming experience. I’m very happy with the Ruckus R650s both in terms of performance, client roaming, and the controller UI is great. A lot of “nerdy” but very useful features, such as built in Wireshark capture engine, great monitoring, and very robust guest WiFi options such as a full captive portal for guests.
I have both APs powered with PoE off the QNAP switch. They pull about 10w each, which is well below the 802.3at 30w PoE maximum.
Pro Tip: If you want the lifetime hardware warranty from Ruckus, only buy your APs through an authorized dealer that will register your APs with Ruckus in your name. Sellers on Amazon and Ebay are NOT authorized. However, several commercial installers have commented Ruckus APs are highly reliable so the chances of needing to use the lifetime warranty are very remote. So Amazon or Ebay could be a viable option.
Firewall Upgrade
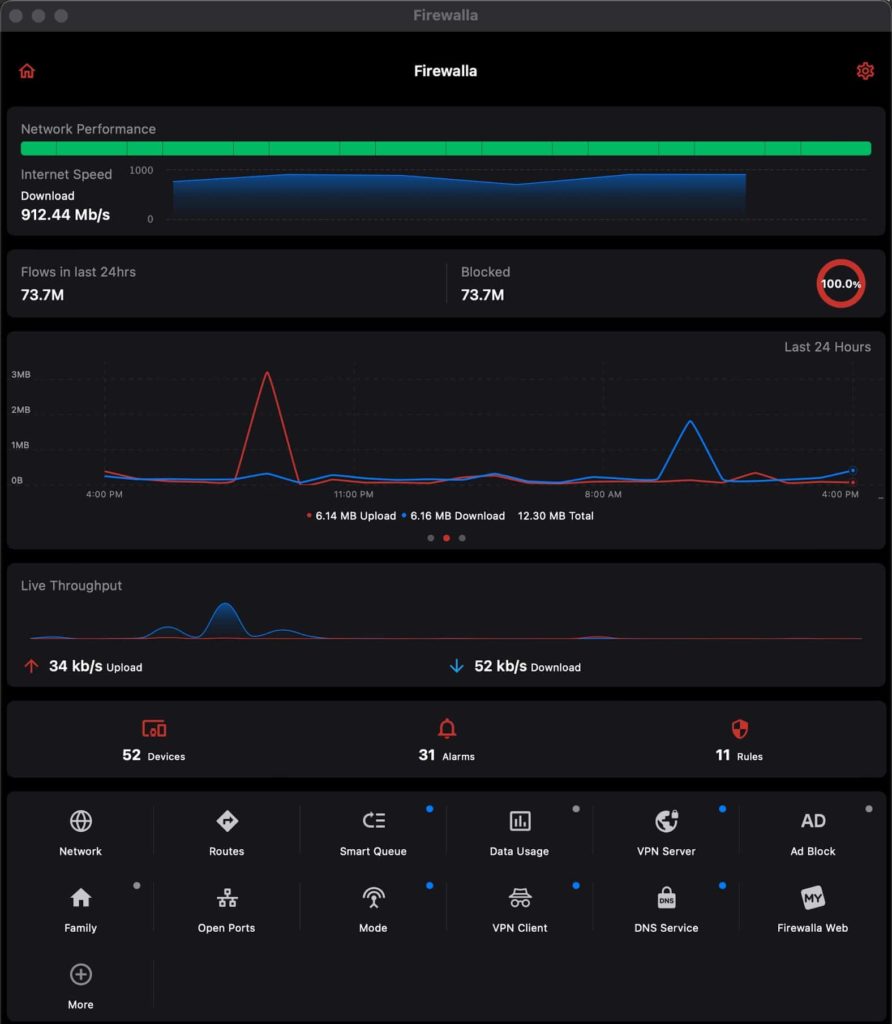
As discussed earlier, my OPNsense firewall felt like a science project. A lot of knobs and features, but not easy to use and very limited traffic insights or security alerts. I also wanted to upgrade to a 2.5Gbps firewall for future proofing. After a lot of research, I ended up with the Firewalla Gold Plus.
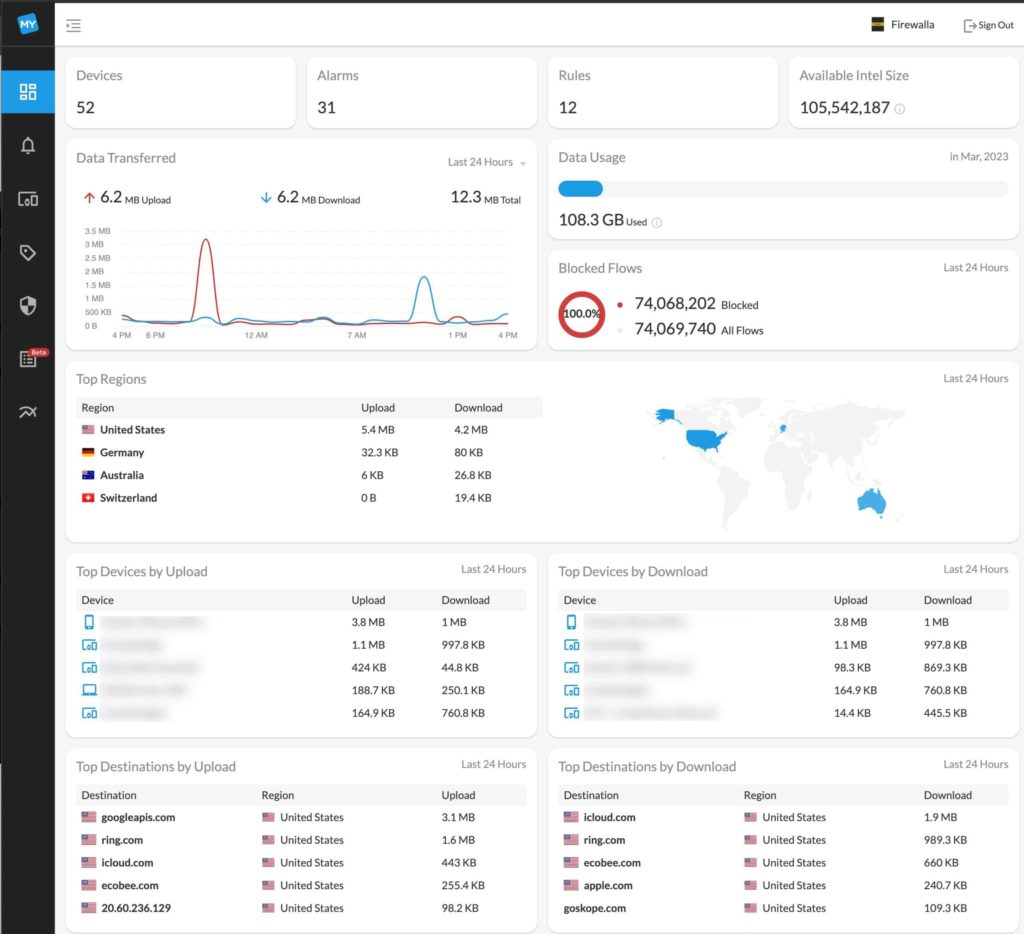
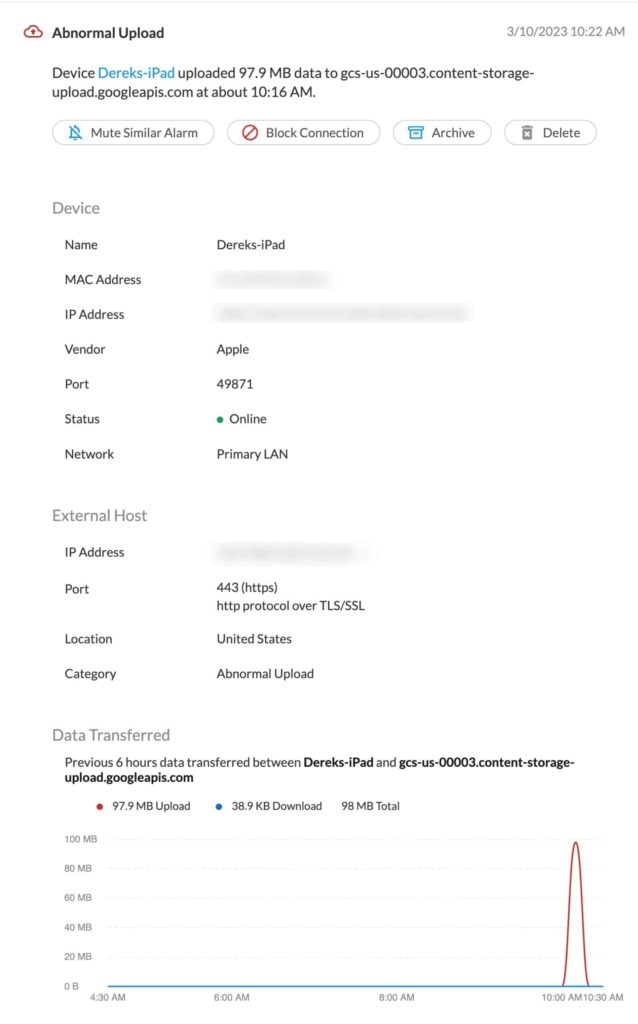
The Gold Plus has been great. Configuration was easy, and what I did in a short afternoon would have taken days of tweaking and troubleshooting with OPNsense. What I really like about the Firewalla is the traffic anomaly alerting. It will detect usual traffic patterns (such as your phone uploading a lot of data to a Google or AWS) and alert you. And it has a lot of advanced features such as VLANs, WAN failover, VPN client/server (Wireguard/OpenVPN), ad blocking, and more.
One quirk of the Firewalla line that I’m not a fan of is their management interface. Their mobile phone or tablet apps are the primary management UI. There’s no local web server interface. You can run the iPad app on your Apple Silicon Mac, which is what I do. They do have a “My Firewalla” web portal, which augments their apps. And if you are a business or service provider, they have a beta (paid) MSP portal that looks pretty sweet. But that’s not aimed at home users with one Firewalla.
If you are a heavy VPN user, the Firewalla supports Wireguard (and OpenVPN) as a VPN client and server. Both can be setup in just a couple of minutes. For the VPN client, you can use any commercial VPN provider that gives you “raw” Wireguard config files. I use ProtonVPN for this. I think Mullvad gives you raw Wireguard config files as well. OpenVPN is an option, but it’s inherently much, much slower.
When the Firewalla is a VPN client, you can setup policy based routing. So certain devices are always routed over the VPN. And it has a VPN kill switch option as well, to prevent traffic leaks.
You can also run the NextDNS CLI directly on the Firewalla. This is basically a cloud based Pi-Hole provider, but with a lot more options. This ensures that all DNS queries are encrypted when they leave my house, so it makes it harder for my ISP to snoop on me or sell my data.
I really like the fact that Firewalla is constantly releasing new updates and features that real people can use. OPNsense felt like their updates were esoteric package updates and no real advancements in features normal people use. My ISP supports IPv6, and so does Firewalla, including DHCP6, which is great.
Summary
My 2023 network upgrade was a total rip and replace of all the switches and patch cables. My core switch is now a QNAP 2.5G/10G PoE switch. WiFi is upgraded to two Ruckus R650 APs. The Firewalla Gold Plus is the new firewall. I’m very happy with the new gear, and it will serve me well for quite a number of years. My Synology is still stuck at 1Gbps NICs, so sometime in the next couple of years that might get an upgrade to take advantage of my multi-gig and 10G network backbone.