I like to perform unattended installations of my operating systems, like Windows Server 2008 R2 or Windows 7 using autounattend.xml so that requires that the image have the required drivers to recognize critical devices like mass storage hardware.
One of the performance optimizations that I always include in our Windows VM templates is the VMware paravirtual SCSI driver. This is a high performance mass storage driver that is optimized for virtual environments and gives you the best disk I/O performance. Unfortunately Microsoft does not include it out of the box on any OS install disk.
So you have two options:
1) Extract boot floppies from an ESXi update. I posted a blog on this a while back. Then you need to mount the virtual floppy image during the Windows install process and manually load the driver. This does not work for an unattended installation as Windows doesn’t automatically look for mass storage drivers.
2) Inject the mass storage drivers directly into the boot.wim file, so it is ‘baked in’ and then you can use an automated Windows install process all while using the high performance SCSI driver. I also inject the drivers into the main OS image (install.wim) so they are available to the operating system after installation.
Since option #2 is more automated, that is of course the option that I want to use. It’s a bit of a complicated process, but in the end in makes life easier. This process can work for other drivers as well, if you also want to use the ISO image on a physical server that has a unique mass storage controller, for instance.
Here is the basic process:
1) You will need to download and install the Windows Automated Installation Kit (WAIK). I used the latest version for Windows 7. Best practices is to install it on a x64 computer, so you can manipulate x64 images should you need to do that.
2) Perform a fully default installation of the WAIK. After the installation is complete, launch the Deployment Tools command prompt.
3) Mount the ISO image of your operating system. Navigate to the Sources directory and copy boot.wim to your computer, say on the D: drive.
4) Create a folder on your D: drive called Drivers. VMware provides both 32-bit and 64-bit pvscsi drivers, and you must use the right one depending on what CPU architecture you are injecting the drivers into. The easiest solution is to leverage an existing 32-bit or 64-bit VM running on vSphere and go into the C:\Program Files\VMware\VMware Tools\Drivers\pvscsi and copy the files in there to D:\drivers.
To verify the supported architecture of the drivers, open the pvscsi.inf file and scroll down to the [Manufacturer] section. If you see NTamd64, you have 64-bit drivers. If you see NTx86, you have 32-bit drivers. The 64-bit pvscsi.sys file is also larger than the 32-bit version (40K vs 35K for vSphere 4.1).
Do not inject both drivers into your image; only use the matching driver for the OS you are modifying. Server 2008 R2 is 64-bit only, whereas you have a choice with Windows 7.
5) Create a folder on the D:\ drive called Mount.
6) In the deployment tool command prompt type:
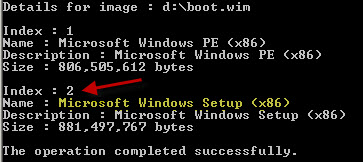
dism /get-wiminfo /wimfile:d:\boot.wim
And look at the index numbers. This is key! You must select index 2, the Windows setup image. If you inject the drivers into index 1, the Windows setup routine will NOT see them and you will be banging your head against the wall.
7) In the deployment tool command prompt type:
dism /Mount-Wim /WimFile:D:\boot.wim /Index:2 /MountDir:D:\mount
8) You should see an operation successful if the image mounted properly.
9) In the deployment tool command prompt type:
dism /image:D:\mount /Add-Driver /driver:d:\drivers\pvscsi.inf
10) You should see an operation successful if the driver was injected properly.
11) Commit the changes and unmount the image with this command:
dism /unmount-wim /mountdir:d:mount /commit
12) At this point I also inject the same drivers into the sourcesinstall.wim file, so the drivers are present before VMware tools gets installed. You follow the same procedure of mounting the WIM, adding the drivers, and then committing the changes. Most install.wim files have multiple images in them, so execute step #6 to list all of the images in the WIM and select the right one(s) to inject the drivers into.
13) Create a backup of your OS ISO file, and then use your favorite ISO editing tool (such as UltraISO) and replace the boot.wim and install.wim files in the Sources directory.
Now you can use the new ISO image to create a VM which uses the pvscsi controller for the boot drive, and you won’t need to manually mount a virtual floppy drive to use a pvscsi boot disk.
If you also want to inject the VMware vmxnet3 drivers, you can use the same procedures. But where do you find the drivers? On a VM running on vSphere navigate to C:\Program Files\VMware\VMware Tools\Drivers\vmxnet3. Copy all of the driver files to the same driver folder from above, and run step #9 a second time, but specifying the vmxnet3ndis6.inf file. Unlike the pvscsi driver, the VMXNET3 driver supports both 32-bit and 64-bit versions with the same set of files.
I would not recommend including the VMware mouse driver (vmmouse.inf) as it’s an unsigned driver and you will get an “Error 50 The request is not supported” when you try and commit the image changes, unless you use the /forceunsigned switch when adding the driver. VMware tools will of course install the mouse driver, so just leave this driver out.
I also wrote a blog about incorporating these drivers into the Windows Recovery environment. This can be very useful if a server goes belly up and you want to try and repair it. You can check that out here.





I struggled a little with this process. With both the current vmxnet3 and pvscsi drivers injected into the Windows Server 2008 R2 installer, I found that installing the VMware tools into the ultimately running VM caused the original vmxnet3 Ethernet adapter to be replaced with vmxnet3 Ethernet adapter 2. This left the first one as a hidden device in the Device Manager and disrupted the static IP configuration. There were no problems with the pvscsi controller. After some trial and error, I settled on injecting only the pvscsi adapter and omitting the injection of the vmxnet3 adapter. I then enabled the vmxnet3 adapter by installing the VMware Tools into the running VM. This issue doesn’t occur with Windows Server 2012.
@jeffry: Interesting..I haven’t seen that problem on 2008 R2 before.
If VMWare tools are installed they have the PV driver and VMXNET3 driver correct?
My reason for asking is we have many VMs already deployed. VM tools is part of the template so has the drivers. not ideal but we are loking to use PV for some drives (not boot drives). are we taking a risk here?
I can't seem to find the paravirtualized SCSI drivers on a Windows 2012R2 VM that is running on an ESXi 5.5 host. Any idea where they might hide?
OK… took me a while to find them. The location has been moved to C:Program FilesCommon FilesVMwareDrivers